Is My Mobile Phone Being Monitored? Part 1/2: Reading The Signs
Most people cannot even imagine that a phone could be monitored. However, by downloading a malicious app, or if a stalker wants to know everything about you, this possibility is not unlikely. In this first part of the "Is My Mobile Phone Being Monitored?" series you can see which signs you need to watch out for, and in the second part you can see what you can do if you have suspicions that your phone is actually being tracked.
How can someone monitor my phone?
Mobile phone technology is growing rapidly, continuously providing users with more and more features. But along with the advantages of this technology, however, many disadvantages become present too.
In older cell phones, before the smartphone era, monitoring capabilities were rather limited (but not non-existent of course). However, modern Android and iOS smartphones can be monitored quite easily with just a single application.

Monitoring methods
There are many ways in which one could monitor your mobile phone. The most basic ones are performed by tapping the device, either by installing software in it or by using special hardware devices.
Phone tapping
Your device can be become tapped even by yourself, through the installation of malware.
You may also become infected with malicious software by receiving it into your device from someone who sent it to your device via bluetooth or sideloading.
Having your phone tapped with a special device points directly to people you know well and trust. It requires the eavesdropper’s physical presence for accessing the phone.
Signal interception
The only method that is very difficult to deal with, and of course refers to services (mainly governmental services) does not concern trapping, but direct signal interception.
What they can do
If your phone is being monitored, it means that the eavesdroppers have access to your calls, chat sessions and text messages.
In addition, they can see photos taken with the device, as well as activate the microphone and listen to all of your private conversations.
If all that sound like conspiracy theories or if you find them normal, or believe that such technology consequently implies monitoring, you probably do not need to read the rest of this guide. You could, though, read the Vault 7 publication in Wikileaks, which includes the recently leaked documents of CIA that thoroughly describe the agency’s monitoring methods.
Who could be monitoring you
Your social and business activities may, objectively, create rivalries, unfair competition, and sometimes, hatred. Thus, it is quite likely that there is someone who wants to know everything about you, either for personal or professional reasons.
A former (or current) jealous partner, or an envious competitor, are candidates who could possibly monitor your phone. They are even likely to outsource the job to a professional, such as a private detective.
Of course, it is much easier for governmental agencies, political parties and government institutions to monitor mobile phones.
Moreover, it is very common (and dangerous) that you might have a malware app installed which is tracking your phone.

The signs
Fortunately though, you do have a way of checking whether your phone is being monitored, and the signs are very specific. Whether you have an Android or iOS device, you can identify if someone has invaded your personal life.
Frequent, unexpected drops during phone calls
Sometimes it might be particularly difficult to make a call due to low signal.
If this phenomenon is becoming more intense over time and happens much more often than what it should under normal conditions, then your phone might be indeed monitored.

Strange noises in the speaker
If you’re hearing uncommon noises during a phone call, or a pulsating static sound, this could be a sign that someone is monitoring your device.
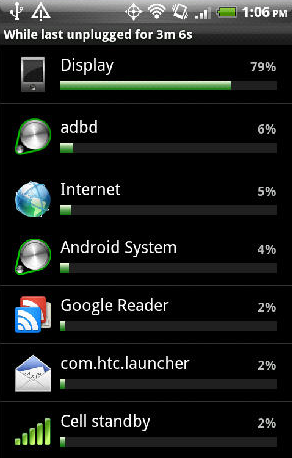
Fast battery drop
Most malicious apps are designed to be active in the background. This makes them constantly active, resulting in drastic battery drops and high temperatures.
If the daily battery drop rate of your device suddenly increases, from one day to another, without having many active applications running in the background, then you should be worried.
Increased temperatures
Another suspicious sign is when the phone’s temperature starts to increase, all out of the blue.
Of course, the temperature rise may be due to excessive use and the large number of active applications, or because of its age.
However, if there are no such reasons, overheating is a sign that your phone is monitored.
Unexplained data usage
Most malware do not just monitor the device; they proceed into stealing sensitive information and data, such as credit card numbers, contact lists, messages etc.
Once they collect the information they want, they use your internet data in order to send the obtained info to some unknown recipient.
If the mobile data becomes enabled by itself, and at the same time an unexplained increase in internet data consumption is observed, then a malicious monitoring app might be the culprit.
Low performance
It is common for most middle-range smartphones to become slower after some months of use.
When this slowdown becomes present in high-end smartphones, which remain slow even after a reboot, it is a sign of malware attack that is consuming resources.
Strange text messages
Some smartphone tracking apps use encrypted text messages, with which they periodically check and control their operation.
These kinds of text messages may be displayed in the form of scrambled characters, such as "#AA24:3AGJ%2". If you see such messages on the device, it is certain that the invasion is in process.
Strange behavior
Sudden device reboots, phone calls and execution of applications without any action from your part, is a worrying sign that your phone might be monitored and someone else is in control.
Another suspicious sign that your device is being monitored is, when, for unexplained reasons, it cannot receive incoming calls and can only make outgoing calls.
Difficulty shutting down the device
If the shutdown process of the device takes a long time, or cannot be completed, then this strange behavior could be an indication that your device is being monitored.
Now that you know what to watch out for in order to check whether your phone is being monitored, you can move on to the second part of the series:
Is My Mobile Phone Being Monitored? Part 2/2: Necessary Actions To Take
If you have any questions or thoughts regarding this topic, don't hesitate to let us know by posting in the comments section below!
