The Experimental Chameleon Worm Wreaks Havoc On Wi-Fi Routers
Developed in a laboratory at the University of Liverpool by Valerio Selis, Johnny Milliken and Prof. Alan Marshall, Chameleon is an experimental virus with the purpose of simulating a malware attack on Belfast and London. Due to the high concentration of Wi-Fi access points (AC) and routers in the metropolises of world, the team of scientists wanted to find out just how vulnerable the residents of large cities are in event of a cyber attack. Given the times we’re living in, the truth is that it’s only a matter of time before you see analogous attacks created by hackers.
Chameleon spreads like an airborne disease
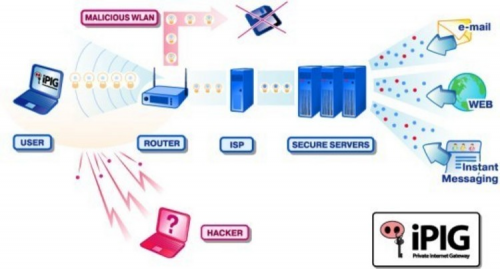
Similar to a highly infectious flu virus, Chameleon spread rapidly among the Wi-Fi networks of the densely populated cities of London and Belfast. Deployed via common access points with poorly secured management interfaces with default passwords, the worm quickly gained access to the network and then attempted to take control of the devices.
Taking control in this case meant replacing the firmware with an open source OpenWrt that allowed the researchers to monitor traffic for credentials and other data. Take note that during the 24 hours experiment, Chameleon was able to avoid detection because it is the first malware of its kind to be present in a Wi-Fi network. Moreover, it was able to do this job undetected by the standard antivirus software.
Once it came across an AP with encryption and password protection, it simply moved on to weaker spots, which it used to hop between networks. This way it managed to infect thousands of devices in a matter of hours.
If you think that the most shocking revelation stemming from this experiment is that a wireless malware threat is real, you are wrong. According to the research team, the most scandalous thing they stumbled across was the incredible number of commercial networks that have weak passwords or don’t rely on passwords and encryption at all. While I can understand weak passwords for a private network, discovering something similar in a commercial one is unacceptable in my book.
…and the good side of the coin
In the form used by the Liverpool researchers, Chameleon cannot migrate beyond the Wi-Fi network and what it actually does is replicate itself, while identifying poorly protected networks. Moreover, because this was just an experiment it doesn't mean you should stop using Wi-Fi spots altogether. As long as you make sure your network is encrypted and protected by a strong password, you can continue utilizing your Wi-Fi network with confidence.