Heartbleed Detection Tools
Heartbleed has been keeping a lot of people on their toes lately – from major services like Elance to small retail e-stores. A lot of people launched changing their passwords just to find out their banking services might not have patched the hole yet. The scenario evolves from bad to worse – now, we hear Android apps and OS itself are vulnerable to Heartbleed, too. But that is not the end of bad news, yet. The worst part, in my opinion, is the news itself. You see, before the news hit the headlines, the vulnerability might have been known to a limited number of people, whereas after the Internet exploded with horror, explaining how Heartbleed actually works, every mediocre wannabe-napster got detailed instructions on how to use Heartbleed vulnerability.
The damage is huge, and it may take years to fix everything that has been affected, so the evil minds have plenty of opportunities to explore the hole. Canadian police was quick enough to arrest a 19 year old self-made programmer, who attacked the Canadian Revenue Agency servers, compromising millions of users’ data. The young ‘entrepreneur’ launched the attack days after the Heartbleed news was released, so chances are we may hear more stories about fun loving kids toying with people’s nightmares.
What can you do in the meantime?
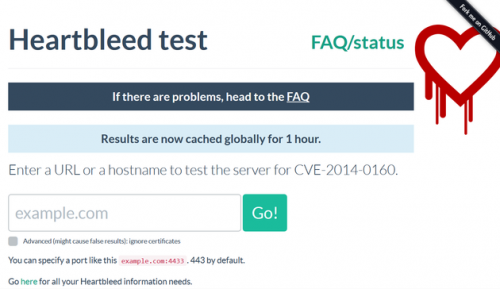
1. Use this Filippo Valsorda website to check other websites for Heartbleed vulnerability.
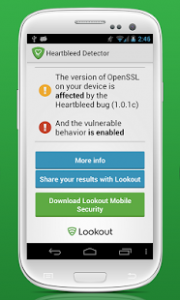
2. Use this Lookout Android app to secure your smartphone.
3. Use common sense – do not open or click on links in emails that come from unknown senders. Also, do not disclose to anyone your password to online banking. Lately, there have been reported mobile scams, where your banks call you requesting your password to reset things and protect you against Heartbleed. Folks, banks don’t do that.
4. Change passwords, and use strong ones this time. Follow this Comprehensive Guide to Secure Passwords.
5. Use browser extensions that check websites you visit for Heartbleed vulnerability:
Chrome
Chromebleed add-on displays a warning if you should treat to websites that haven’t patched their OpenSSL vulnerability yet. This add-on relies on the above-mentioned Filippo Valsorda website to run the check of the URLs.
Firefox
FoxBleed add-on is similar to the above-mentioned Chromenleed, and it also checks for Heartbleed vulnerability automatically via the same Filippo Valsorda service, notifying you if the threat is detected. The add-on checks the entered domain name only once per browser session.
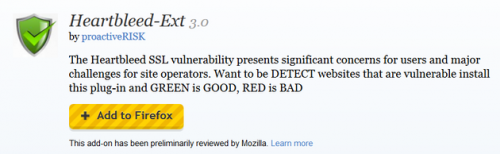
Heartbleed-Ext add-on works according to the same pattern, checking the URLs at Filippo Vaslorda website, displaying a notification if the threat is detected: green – go, red – stop.
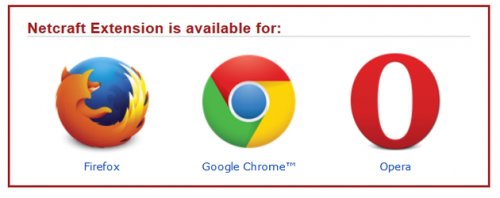
Chrome, Firefox, Opera
Netcraft offers Heartbleed detecting add-on for Chrome, Firefox and Opera, so you can navigate to their website and choose the extension for your browser.
I haven’t found any extension for IE or Safari, yet, so you are welcome to contribute in the comments below.
Browser Settings
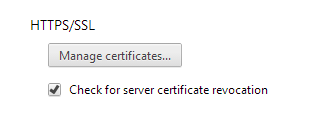
Chrome
Go to Settings -> Advanced Settings -> HTTP/SSL -> check the box next to “Check for server certificate revocation.”
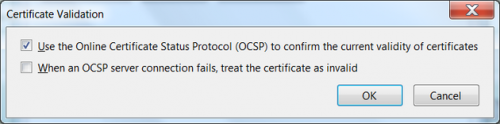
Firefox
You can enable hard-fail in Firefox, but this method has its disadvantages. If you know what you are doing, you can go to Options -> Advanced ->Certificates -> Validation -> check the box next to “When an OCSP server connection fails, treat the certificate as invalid."
Final Words
Please, be aware the add-ons may give false positives, but you are better off double-checking before doing any financial transactions online.